- Remote Desktop Services - Multi-Factor Authentication ..
- Windows Server 2016 Remote Desktop Services Cal

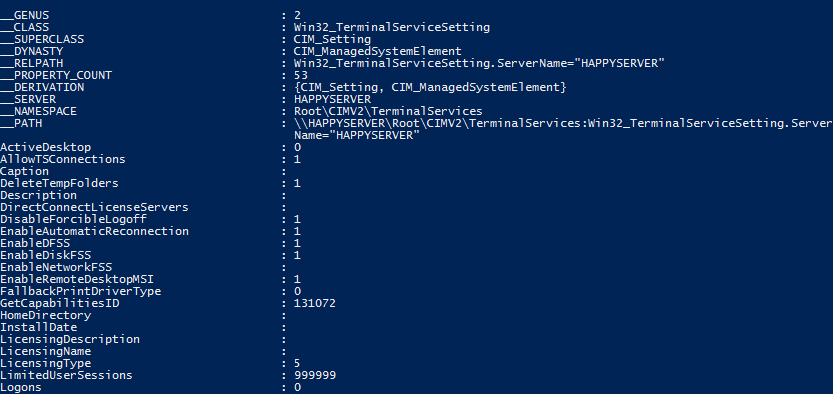
This is a comprehensive guide for installing RDS services to a Windows Server 2016. We will see in great detail how to enable the Remote Desktop Roles, Activate the RDS licenses and make the final configuration to make it work. This chapter presents Windows Server Remote Desktop Services (RDS), which enables remote access to operating systems, both server and desktop, with the primary goal of providing users with a desktop experience. As I will explain, you can achieve this in various ways, and this chapter focuses on where Hyper-V is critical. We have now setup Remote Desktop Services for Windows Server 2016. In this type of Remote Desktop Services setup, the clients will Remote Desktop directly to the RD Session Host server that is part of the collection to use the applications that are installed on the RD Session Host server.
-->Remote Desktop Services (RDS) is the platform of choice for building virtualization solutions for every end customer need, including delivering individual virtualized applications, providing secure mobile and remote desktop access, and providing end users the ability to run their applications and desktops from the cloud.
RDS offers deployment flexibility, cost efficiency, and extensibility—all delivered through a variety of deployment options, including Windows Server 2016 for on-premises deployments, Microsoft Azure for cloud deployments, and a robust array of partner solutions.
Remote Desktop Services - Multi-Factor Authentication ..
Depending on your environment and preferences, you can set up the RDS solution for session-based virtualization, as a virtual desktop infrastructure (VDI), or as a combination of the two:
- Session-based virtualization: Leverage the compute power of Windows Server to provide a cost-effective multi-session environment to drive your users' everyday workloads.
- VDI: Leverage Windows client to provide the high performance, app compatibility, and familiarity that your users have come to expect of their Windows desktop experience.
Within these virtualization environments, you have additional flexibility in what you publish to your users:
- Desktops: Give your users a full desktop experience with a variety of applications that you install and manage. Ideal for users that rely on these computers as their primary workstations or that are coming from thin clients, such as with MultiPoint Services.
- RemoteApps: Specify individual applications that are hosted/run on the virtualized machine but appear as if they're running on the user's desktop like local applications. The apps have their own taskbar entry and can be resized and moved across monitors. Ideal for deploying and managing key applications in the secure, remote environment while allowing users to work from and customize their own desktops.
For environments where cost-effectiveness is crucial and you want to extend the benefits of deploying full desktops in a session-based virtualization environment, you can use MultiPoint Services to deliver the best value.
With these options and configurations, you have the flexibility to deploy the desktops and applications your users need in a remote, secure, and cost-effective fashion.
Next steps
Here are some next steps to help you get a better understanding of RDS and even start deploying your own environment:
- Understand the supported configurations for RDS with the various Windows and Windows Server versions
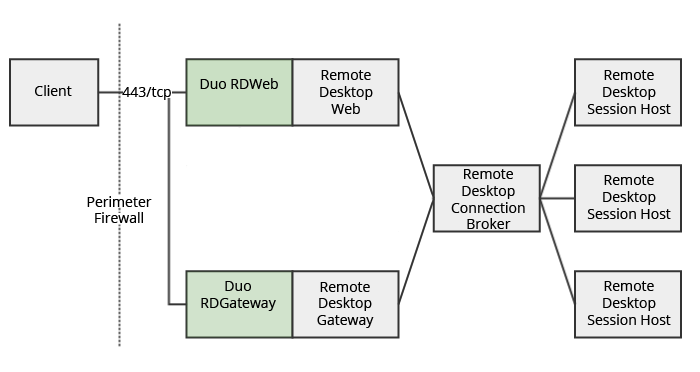
- Plan and design an RDS environment to accommodate various requirements, such as high availability and multi-factor authentication.
- Review the Remote Desktop Services architecture models that work best for your desired environment.
- Start to deploy your RDS environment with ARM and Azure Marketplace.
Applies To: Windows Server 2016, Windows Server 2019
When it comes to supported configurations for Remote Desktop Services environments, the largest concern tends to be version interoperability. Most environments include multiple versions of Windows Server - for example, you may have an existing Windows Server 2012 R2 RDS deployment but want to upgrade to Windows Server 2016 to take advantage of the new features (like support for OpenGLOpenCL, Discrete Device Assignment, or Storage Spaces Direct). The question then becomes, which RDS components can work with different versions and which need to be the same?
So with that in mind, here are basic guidelines for supported configurations of Remote Desktop Services in Windows Server.
Note
Make sure to review the system requirements for Windows Server 2016 and system requirements for Windows Server 2019.
Best practices
Use Windows Server 2019 for your Remote Desktop infrastructure (the Web Access, Gateway, Connection Broker, and license server). Windows Server 2019 is backward-compatible with these components, which means a Windows Server 2016 or Windows Server 2012 R2 RD Session Host can connect to a 2019 RD Connection Broker, but not the other way around.
For RD Session Hosts - all Session Hosts in a collection need to be at the same level, but you can have multiple collections. Download free iphoto mac. You can have a collection with Windows Server 2016 Session Hosts and one with Windows Server 2019 Session Hosts.
If you upgrade your RD Session Host to Windows Server 2019, also upgrade the license server. Remember that a 2019 license server can process CALs from all previous versions of Windows Server, down to Windows Server 2003.
Follow the upgrade order recommended in Upgrading your Remote Desktop Services environment.
If you are creating a highly available environment, all of your Connection Brokers need to be at the same OS level.
RD Connection Brokers
Windows Server 2016 removes the restriction for the number of Connection Brokers you can have in a deployment when using Remote Desktop Session Hosts (RDSH) and Remote Desktop Virtualization Hosts (RDVH) that also run Windows Server 2016. The following table shows which versions of RDS components work with the 2016 and 2012 R2 versions of the Connection Broker in a highly available deployment with three or more Connection Brokers.
| 3+ Connection Brokers in HA | RDSH or RDVH 2019 | RDSH or RDVH 2016 | RDSH or RDVH 2012 R2 |
|---|---|---|---|
| Windows Server 2019 Connection Broker | Supported | Supported | Supported |
| Windows Server 2016 Connection Broker | N/A | Supported | Supported |
| Windows Server 2012 R2 Connection Broker | N/A | N/A | Not Supported |
Support for graphics processing unit (GPU) acceleration
Remote Desktop Services support systems equipped with GPUs. Applications that require a GPU can be used over the remote connection. Additionally, GPU-accelerated rendering and encoding can be enabled for improved app performance and scalability.
Remote Desktop Services Session Hosts and single-session client operating systems can take advantage of the physical or virtual GPUs presented to the operating system in many ways, including the Azure GPU optimized virtual machine sizes, GPUs available to the physical RDSH server, and GPUs presented to the VMs by supported hypervisors.
See Which graphics virtualization technology is right for you? for help figuring out what you need. For specific information about DDA, check out Plan for deploying Discrete Device Assignment.
GPU vendors may have a separate licensing scheme for RDSH scenarios or restrict GPU use on the server OS, verify the requirements with your favorite vendor.
GPUs presented by a non-Microsoft hypervisor or Cloud Platform must have drivers digitally-signed by WHQL and supplied by the GPU vendor.
Remote Desktop Session Host support for GPUs
The following table shows the scenarios supported by different versions of RDSH hosts.
| Feature | Windows Server 2008 R2 | Windows Server 2012 R2 | Windows Server 2016 | Windows Server 2019 |
|---|---|---|---|---|
| Use of hardware GPU for all RDP sessions | No | Yes | Yes | Yes |
| H.264/AVC hardware encoding (if suppported by the GPU) | No | No | Yes | Yes |
| Load balancing between multiple GPUs presented to the OS | No | No | No | Yes |
| H.264/AVC encoding optimizations for minimizing bandwidth usage | No | No | No | Yes |
| H.264/AVC support for 4K resolution | No | No | No | Yes |
VDI support for GPUs
The following table shows support for GPU scenarios in the client OS.
| Feature | Windows 7 SP1 | Windows 8.1 | Windows 10 |
|---|---|---|---|
| Use of hardware GPU for all RDP sessions | No | Yes | Yes |
| H.264/AVC hardware encoding (if suppported by the GPU) | No | No | Windows 10 1703 and later |
| Load balancing between multiple GPUs presented to the OS | No | No | Windows 10 1803 and later |
| H.264/AVC encoding optimizations for minimizing bandwidth usage | No | No | Windows 10 1803 and later |
| H.264/AVC support for 4K resolution | No | No | Windows 10 1803 and later |
RemoteFX 3D Video Adapter (vGPU) support
Note
Because of security concerns, RemoteFX vGPU is disabled by default on all versions of Windows starting with the July 14, 2020 Security Update and removed starting with the April 13, 2021 Security Update. To learn more, see KB 4570006.
Windows Server 2016 Remote Desktop Services Cal
Remote Desktop Services supports RemoteFX vGPUs when VM is running as a Hyper-V guest on Windows Server 2012 R2 or Windows Server 2016. The following guest operating systems have RemoteFX vGPU support:
- Windows 7 SP1
- Windows 8.1
- Windows 10 1703 or later
- Windows Server 2016 in a single-session deployment only
Discrete Device Assignment support
Remote Desktop Services supports Physical GPUs presented with Discrete Device Assignment from Windows Server 2016 or Windows Server 2019 Hyper-V hosts. See Plan for deploying Discrete Device Assignment for more details. Download musescore on macbook air.
VDI deployment – supported guest OSes
Windows Server 2016 and Windows Server 2019 RD Virtualization Host servers support the following guest OSes:
- Windows 10 Enterprise
- Windows 8.1 Enterprise
- Windows 7 SP1 Enterprise
Note
- Remote Desktop Services doesn't support heterogeneous session collections. The OSes of all VMs in a collection must be the same version.
- You can have separate homogeneous collections with different guest OS versions on the same host.
- The Hyper-V host used to run VMs must be the same version as the Hyper-V host used to create the original VM templates.
Single sign-on
Windows Server 2016 and Windows Server 2019 RDS supports two main SSO experiences:
- In-app (Remote Desktop application on Windows, iOS, Android, and Mac)
- Web SSO

Using the Remote Desktop application, you can store credentials either as part of the connection info (Mac) or as part of managed accounts (iOS, Android, Windows) securely through the mechanisms unique to each OS.
To connect to desktops and RemoteApps with SSO through the inbox Remote Desktop Connection client on Windows, you must connect to the RD Web page through Internet Explorer. The following configuration options are required on the server side. No other configurations are supported for Web SSO: Software download for macbook air epson elpdc06.
- RD Web set to Forms-Based Authentication (Default)
- RD Gateway set to Password Authentication (Default)
- RDS Deployment set to 'Use RD Gateway credentials for remote computers' (Default) in the RD Gateway properties
Note
Due to the required configuration options, Web SSO is not supported with smartcards. Users who login via smartcards might face multiple prompts to login.
For more information about creating VDI deployment of Remote Desktop Services, check out Supported Windows 10 security configurations for Remote Desktop Services VDI.
Using Remote Desktop Services with application proxy services
You can use Remote Desktop Services with Azure AD Application Proxy. Remote Desktop Services does not support using Web Application Proxy, which is included in Windows Server 2016 and earlier versions.
